Using the Event Grid Service in a Private Context to Prevent Intrusions

Systems integration is now a must-have for modern businesses. Integration solutions like Azure Event Grid, an Azure Integration Service (AIS) platform product, offer flexible ways to connect different types of systems, automate workflows, and improve operational efficiency.
However, because cyberattacks and data breaches are becoming more common, it is essential to take the proper security steps to protect the sensitive data that moves between these systems. In this post, we’ll discuss best practices for using Azure Event Grid securely, focusing on how important security is for integration solutions.
If you want to learn more about Event Grid but haven’t worked with it yet, take a look at our previous post (written in French), “Azure Integration Platform As A Service (IPaaS): How to Manage Your Events with Azure Event Grid & Logic Apps.”
How to Keep Azure Event Grid Data Secure
Azure Event Grid involves sending and receiving events in near-real time to synchronize data with third-party systems and/or within a highly decoupled system.
With this easy communication comes increased security risks. For example, events passing through Azure Event Grid may contain sensitive data like user credentials or financial transaction data. So, it’s vital to protect this data during transmission.
Use the following methods to ensure data passing through Azure Event Grid is secure:
- Secure communication methods (data encryption), such as HTTPS;
- Managed identities for event subscriptions to make sure only authorized users/applications can access the data;
- Suitable network configuration and privatization based on a VNet or a private link/private endpoint;
- Built-in Azure Event Grid definitions (Azure policies);
- Logging and monitoring can help detect and prevent attacks before they cause any damage.
Event Grid and Private Network Security: Capabilities and Limitations
Setting up a private network in the cloud is critical to ensuring security and confidentiality and, most importantly, preventing corporate data leaks.
Private Endpoints (Event Publishing)
Private endpoints provide a secure solution for publishing events from your virtual network (VNet) straight to custom topics without going through the public network. Instead, the private link creates a private connection between the VNet and the custom topic, and the private endpoint talks to the topic using a private IP address from the VNet address space.

Using the private endpoint for Event Grid lets you:
- Secure access to the topic through a virtual private network (VNet) rather than public access
- In a hybrid infrastructure (site-to-site VPN or ExpressRoute), secure access from the company’s local network
Note:
- The publishers (event sources) sending events to the virtual network (VNet) using a private endpoint must use the same connection string to connect through the public network (no change).
- DNS resolution automatically routes connections from the VNet to the topic via a private link. By default, Event Grid creates a private DNS zone linked to the VNet with the necessary updates for the private endpoints.
- The VPN hosting the private endpoint handles DNS resolution, and the private endpoint’s IP address is used to resolve the topic URL. When resolved from the VNet hosting the private endpoint, the DNS resource records for a topic named “topicEX”, for example, will be as follows:
| Name | Type | Value |
| topicEX.westus.eventgrid.azure.net | CNAME | topicEX.westus.privatelink.eventgrid.azure.net |
| topicEX.westus.privatelink.eventgrid.azure.net | A | 10.0.10.6 |
Here is a link to the steps for configuring an Event Grid private endpoint.
IP Firewall
Even if authentication and valid authorization are required, Event Grid topics can be accessed from the Internet by default. Access to the network, on the other hand, remains public.
So, you can reduce the risk of distributed denial-of-service (DDoS) and other injection attacks by using Azure network firewall rules to limit access to event subscriptions to specific IP addresses only. Azure network firewall rules also help make sure that only authorized users/applications can access your Event Grid. This provides an added layer of protection for your valuable data.
Publishers (event sources) from other IP addresses not authorized within the firewall will be rejected and get an HTTP 403 response. Have a look at the Microsoft documentation to find out step-by-step how to set up the IP Event Grid firewall.
Is It Possible to Deliver Events through Private Endpoints?
Microsoft has said (most recently on 03/02/2023) that Event Grid does not support event delivery to private resources through private endpoints. In other words, there is no support if you have strict network isolation requirements where your delivered events traffic must not leave your VNet.
To overcome this limitation, Microsoft suggests setting up middleware to send events to services such as Event Hub, Service Bus, or Azure Storage, using system-assigned or user-assigned managed identities.
Then, to receive the events, you need to set up a private link in Azure Functions or have your webhook set up in your VNet.
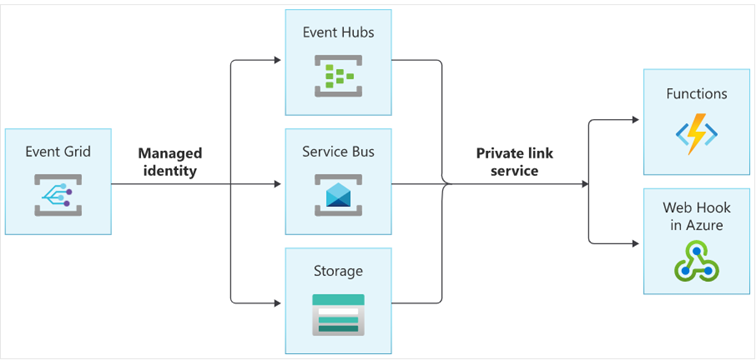
With this configuration, traffic between Azure Event Grid and Event Hubs, Service Bus, or Azure Storage stays in the Microsoft Azure backbone and uses a managed identity.
By configuring a webhook or Azure Function in the VNet to use Event Hubs, Service Bus or Azure Storage via a private endpoint, traffic between these services and the webhook or Azure Function stays within the VNet perimeter.
This configuration makes the integration solution more secure because only authorized VNet users can access the data going through these services. It also reduces the risks involved in sending data over the Internet.
Here is the Microsoft documentation on event delivery with a managed identity if you want to learn more.
Event Grid: Key Takeaways
By using the best practices in this post, you can make your Azure Event Grid-based integration solution more secure and reduce the risks of a data breach.
Lastly, data security is a significant concern for businesses and organizations of all sizes. Therefore, it is crucial to implement appropriate security measures to protect sensitive data from cyberattacks and data breaches. Azure Event Grid has features like network access configuration and managed identity and access management (access-control lists – ACLs) that can be used to ensure event security.