Delegating User and Device Management in Azure AD and Intune

Today’s post aims to answer the following question: How do you delegate user and device management to regional administrators within a multi-region organization?
The first section will introduce the “administrative unit” concept in Azure Active Directory. You can use this resource to delegate user administration roles to the regional support team, allowing them to manage only the users within their region.
The second section discusses Role-Based Access Control (RBAC) and scope tags in endpoint management (Intune). This feature can delegate device management to local IT support teams. They will only have the ability to manage devices in their region.
Administrative Units in Azure AD
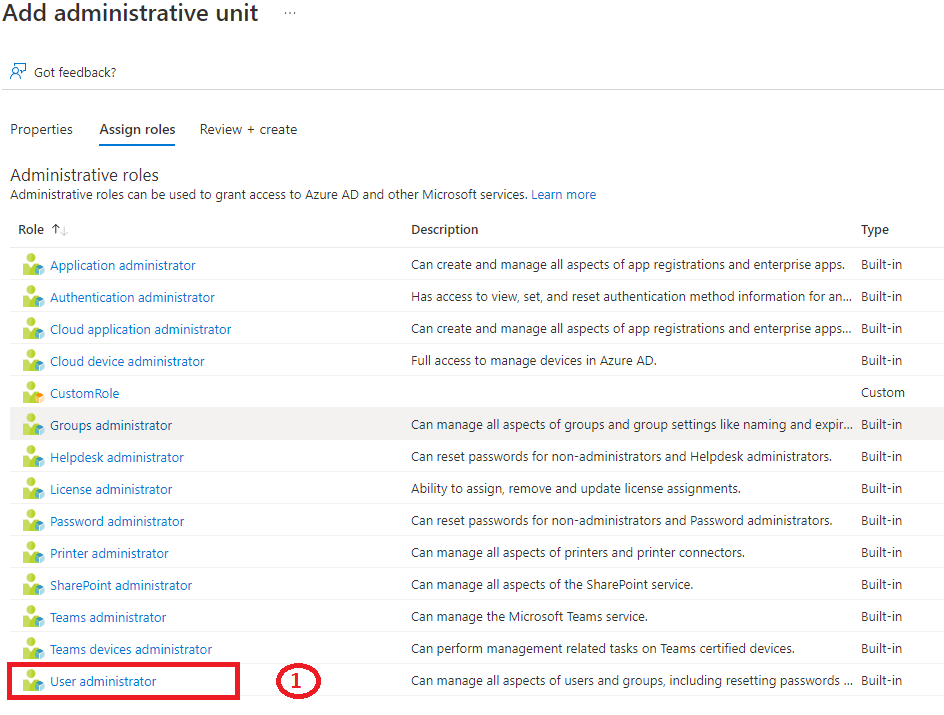
Administrative units are containers that allow you to group users and machines (PC, smartphone, tablet, etc.). These objects can be assigned to these containers dynamically or manually. After you’ve assigned the objects, you need to assign administrators a role from the predefined options. You can also create a custom role and assign it to the administrator.

Our case study is a multinational organization with a presence across several regions (France, Tokyo, USA, Australia).
Here is an example of creating an administrative unit for the France region.
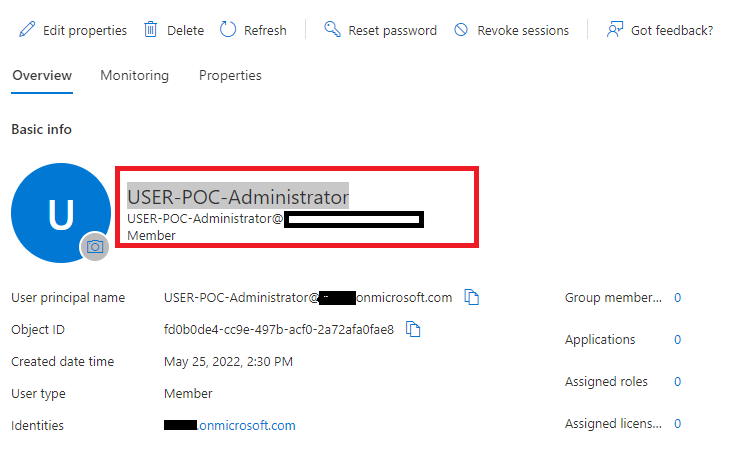
1. Create a user named “USER-POC-Administrator” to manage the France administrative unit (AU) users.
2. In the Azure AD portal, select “Administrative unit” => Add.

In “Assign roles,” choose “User administrator” and select the user you created in step 1:
Finally, click Create.

3. To assign users to the administrative unit you just created, click “AU-AAD-France-Users,” then “Users,” and “Add members,” then select the users or groups.
Change the administrative unit type to “Dynamic” to assign users dynamically and create an assignment rule.
Click “AU-AAD-France-Users” => Properties => and change the type to “Dynamic User”:
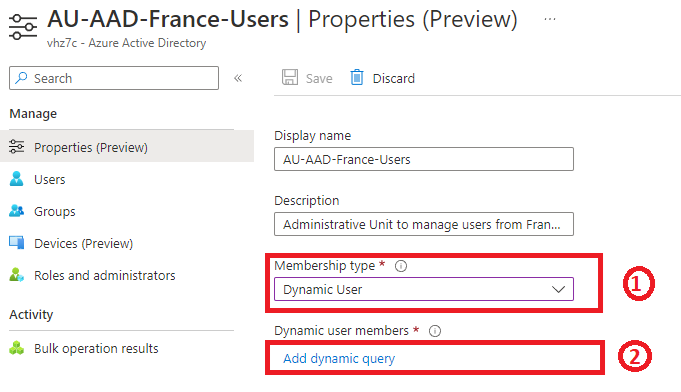
The dynamic rule for selecting users from France where the country property == France is as follows: (user.country -contains “France”).
Any user whose country property == France will be dynamically assigned to the “AU-AAD-France-Users” administrative unit.
The “USER-POC-Administrator” administrator will manage the “AU-AAD-France-Users” AU users. The latter will have all of the “User Administrator” role permissions, such as being able to reset passwords, change properties, assign licenses, etc.
Other regional administrators can view the users in the “AU-AAD-France-Users” AU, but they do not have admin rights. The AU must be created by code using Microsoft Graph to hide users from other regional administrators. The “visibility” property controls whether the administrative unit and its members are hidden or visible. When the value is set to “HiddenMembership,” only members of the administrative unit can list other members of the administrative unit.
Here is the code for a function in Python that creates an administrative unit with the “HiddenMembership” option:

Endpoint Management (Intune) RBAC and Scope Tag
Role-based access control (RBAC) and scope tags can be used in Intune to ensure that the right administrators can see and access the objects they manage. Roles determine an administrator’s permissions, and scope tags determine which objects an administrator can see.
Let’s look at the example of a multi-region organization. Each region has its own IT support team for PC management. We want the administrators of the “France” region to have complete control over all the PCs in that region, with the ability to:
- Apply updates
- Apply a configuration profile
- Audit PCs based on a compliance strategy
- Configure Defender for Endpoint, Bitlocker, and Windows Firewall
- Restart, scan, and inventory
Here’s what you need to do to meet these requirements:
Step 1: In Azure AD
- Create a security group and add all PCs in the France region to it by assigning them directly or dynamically to the “GR-AAD-France-DeviceList.”

- Create a security group called “GR-AAD-France-Devices-Administrators” for device administrators in the “France” region.

Step 2: In Intune
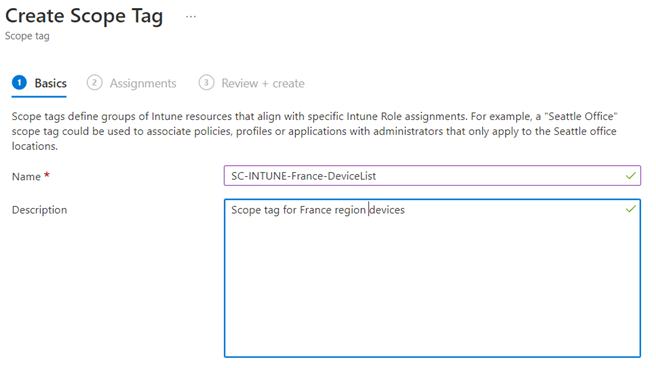
- Create a scope tag for the “GR-AAD-France-DeviceList” group. In the Intune admin center è Tenant administration è Roles è Scope tag, create “SC-INTUNE-France-DeviceList.”
In “Assignments,” add the “GR-AAD-France-DeviceList” group.

- Create an Intune role
In “Role”, click “Add”

Choose from the list of permissions:

In “Scope tags”, select “SC-INTUNE-France-DeviceList” and click “Create.”
Choose the role you created earlier from the list of roles, then click “Assignment” to add “ASS-INTUNE-France-Device-Administrator” as a new assignment.

In the “Admin Groups” tab, select the “GR-AAD-France-Devices-Administrators” group.

In “Scope Groups”, select “GR-AAD-France-DeviceList.”

Finally, in “Scope tags”, select the “SC-INTUNE-France-DeviceList” scope.

By signing in to the Intune portal with a user ID that belongs to the “GR-AAD-France-Devices-Administrators” group (e.g., USER-POC-Administrator), and in accordance with the permissions assigned to them, the user will only be able to see and manage PCs that belong to the “GR-AAD-France-DeviceList” group.
The “France” region administrator can only assign a new compliance strategy to its “SC-INTUNE-France-DeviceList” scope when creating it.

Would you like to learn more about cloud security? Be sure to read all the posts in this brand-new series written by our experts: